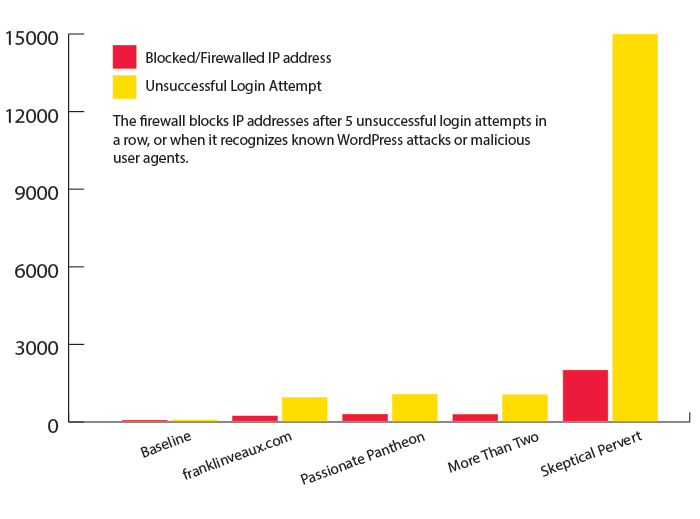
NOTE: This blog post was updated on January 25, 2025. Update at end.
If you own a website that uses stock images or even images you’ve taken yourself, beware a scam floating around that tries to trick you into putting links to another site on your pages.
I recently received a phony “DMCA Copyright Infringement Notice” run by a scammer attempting to get backlinks to a site called KnowYourSins, a sex site run by two people named Samuel Davis (@Samueld_KYS on Twitter) and Olivia Moore (@Olivia_kys on Twitter).
The letter claims to come from a law firm called “Commonwealth Legal Services” in Phoenix, Arizona. Here’s a screenshot:

So, the first thing to know about this email is it’s very unusual for a DMCA complaint, which is almost always a takedown request, not a request for a backlink.
The second thing to notice is there’s a standard format for DMCA takedowns, and they must, by law, include:
- Information reasonably sufficient to permit the service provider to contact the complaining party, such as an address, telephone number, and e-mail address.
- A statement that the complaining party has a good faith belief that use of the material in the manner complained of is not authorized.
- A statement that the information in the notification is accurate, and under penalty of perjury, that the complaining party is authorized to act on behalf of the copyright holder.
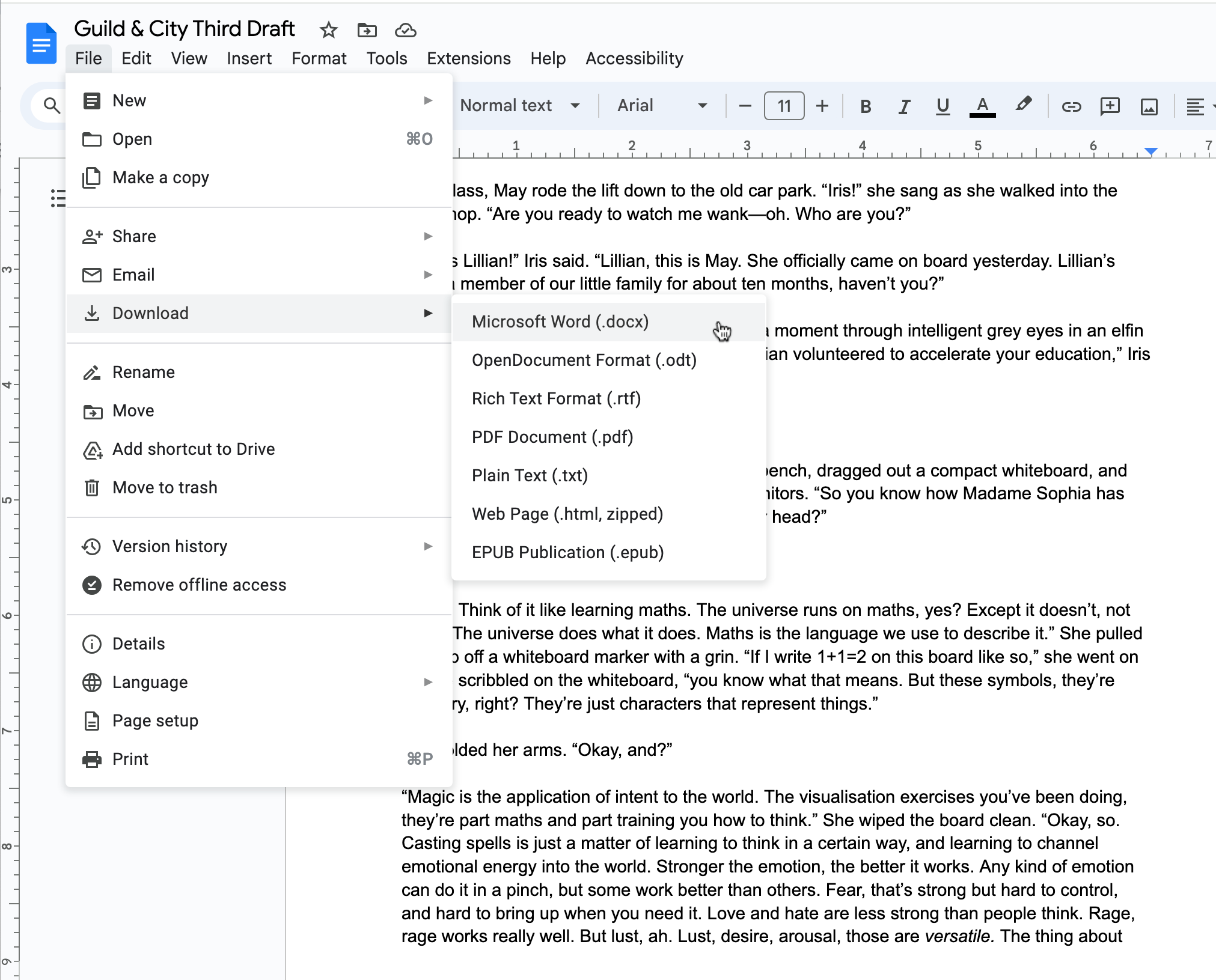
The image itself comes from Unsplash, specifically this one, and it was taken by Eric Lucatero, who has no connection with KnowYourSins dot com.

Huh.
Commonwealth Legal Services
I looked at the website of the supposed “law firm” that sent it, justicesolutionshub.info. Now, the fact that it uses a .info top-level domain immediately set off warning bells in my head as well.
“Zoe Baker” signs this email “Trademark Attorney,” yet the page on justicesolutionshub.info lists “her” as a “business legal consultant.”

Huh.
On top of that, notice anything funny about all these headshots? Look closely.
Yup, they’re all generated by AI—specifically, they all come from This Person Does Not Exist.
How can you tell?
AI deepfake faces generated by This Person Does Not Exist always have eyes in exactly the same place exactly the same size and exactly the same distance apart. It’s a limitation of the adversarial GAN software that creates the fake faces.
You can see it if you stack the faces on top of each other and make them translucent in Photoshop.

I looked up “Commonwealth Legal Services” on Google. It turns out there are a bunch of different websites at different URLs all using the same exact web design with the same copy and the same pictures: justicesolutionshub.info, cwsolutions.biz, elitejusticeadvisors.biz (currently offline), and more.
The front page of justicesolutionshub.info shows a photo of a building. The office building is a stock photo rendering that you can put any logo in front of.

This is an Adobe Photos stock photo rendering created by digital artist “Esin.” A surprising number of phony fly-by-night bogus “companies” use this stock image as their corporate headquarters on their About or Contact pages.

Things really take a turn for the surreal if you put the address of “Commonwealth Legal Services,” 3909 N. 16th Street, Fourth Floor, Phoenix, AZ 85016 into Google Street View. This one weird trick produced results you aren’t going to believe:

Note the conspicuous absence of a fourth floor. As of the time of writing this, the building is currently listed for sale.
Okay, so we have a fake DMCA takedown request from a phony law office attempting to blackmail me into putting a backlink to Know Your Sins from my site.
Know Your Sins
So, what is Know Your Sins?
It’s a more or less generic BDSM information site with precious little in the way of in-depth information, using largely AI-generated content and stock photos.

I can see a couple of possibilities:
- Know Your Sins is scamming in a desperate bid to attract backlinks and improve their search engine ranking.
- Know Your Sins is a victim; they hired a dodgy “we can boost your search engine ranking” scammer, not knowing that he was engaging in fraud.
I emailed the contact address at Know Your Sins, hello (at) knowyoursins (dot) com, to try to get some insight. So far, as of the time of writing this, I have not received a reply. I will update this blog post if they get back in touch with me.
I’ve also been in touch with several webmasters who have received identical DMCA complaints, at least one of whom was accused of pirating a photo he took, all with demands to link back to Know Your Sins.
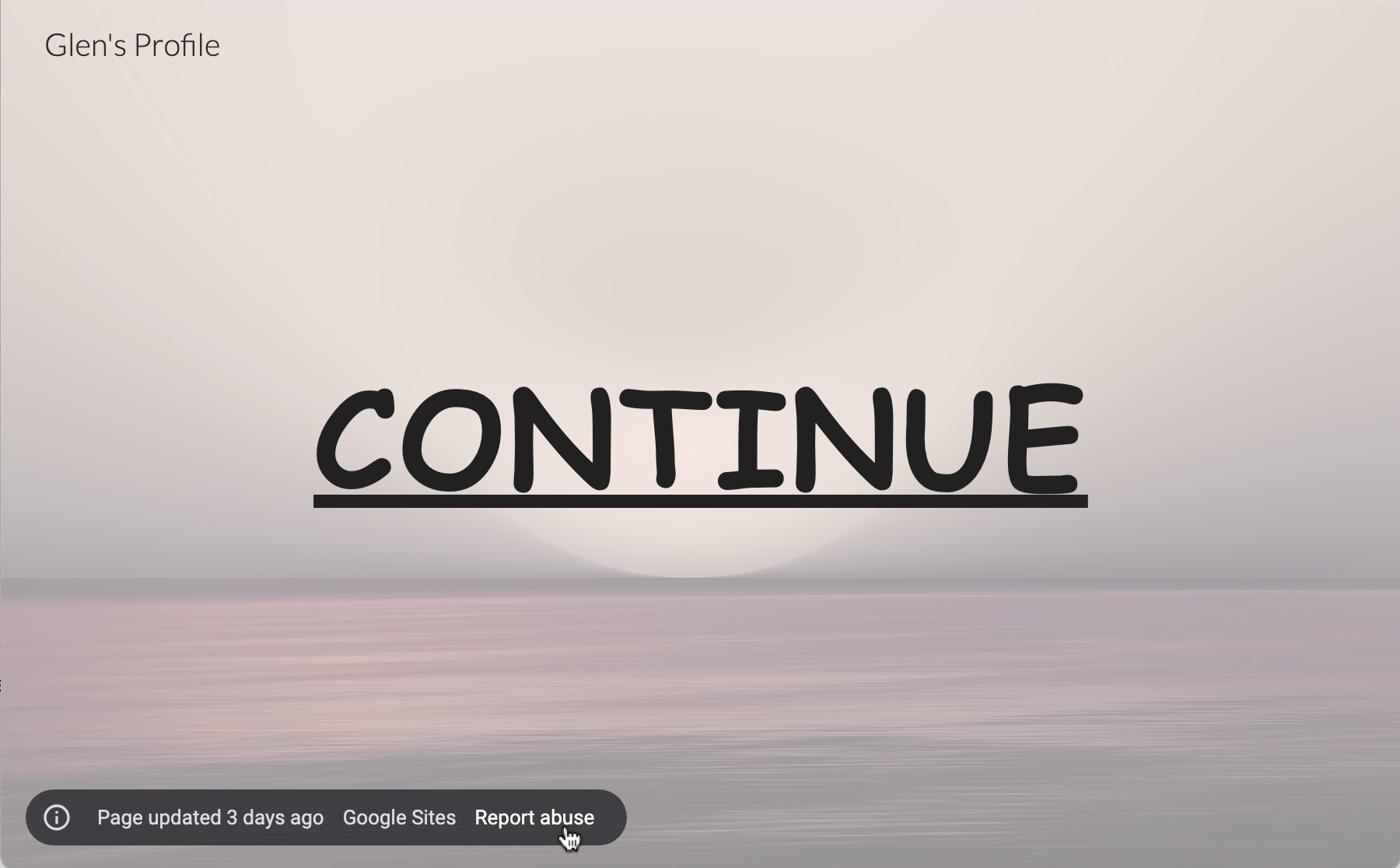
The Know Your Sins domain registration is hidden by Privacy protect. I’ve filed a formal complaint with them, since they claim they’ll rescind the privacy protection on sites that engage in spamming or fraud. (I urge anyone who’s received one of these scam emails to do the same using the “report abuse” form here.) If they reply, I’ll post the results.
Isn’t there a penalty for false DMCA takedown requests?
No. Perhaps surprisingly, there isn’t.
There are penalties for impersonating a lawyer, and for fraud. The emails are definitely fraud, and I do not for even half a second believe the person sending them is a lawyer, so there may be avenues of legal action there. I suspect, given that others are reporting these emails but they don’t always demand a link to Know Your Sins (some of them demand links to other sites), that what’s most likely happening is a scammer is selling his services to desperate website owners who want more Google linkbacks but don’t care too much if they’re totally on the up and up.
The lesson here
Genuine DMCA takedown requests must follow a certain specific legal format (including a statement that under penalty of perjury, the person sending the request has a good-faith belief that the claimed infringement is genuine), and don’t ask for linkbacks.
If you get a “DMCA warning” or “DMCA takedown” that asks you to link to another site, you’re being scammed.
If you’ve received one of these fake takedown requests, I’d love to hear from you! I’m in the process of trying to strip the Privacy Protection from the knowyoursins domain registration, and the more examples I have, the better. Please feel free to email me at franklin (at) franklinveaux (dot) com.
UPDATE JANUARY 25, 2025
A lot of people have sent me copies of similar fake DMCA emails demanding linkbacks to knowyoursins dot com. The site is registered at GoDaddy. This morning, I had a long and interesting conversation with a member of the GoDaddy abuse team, who has told me that GoDaddy is opening an investigation into knowyoursins dot com for fraudulent DMCA takedowns and fraudulent backlink farming.
Have you received a “DMCA takedown” demanding a link to knowyoursins dot com? GoDaddy’s abuse team would like to hear from you.
Please visit the GoDaddy abuse reporting form at
https://supportcenter.godaddy.com/abusereport
Create a new report, choose the “Phishing” option, and in the details section, put a copy of the fraudulent email you received, with a brief explanation that you are reporting the site for fraudulent DMCA takedowns and fraudulent backlink farming.
And, of course, I’d love to see copies of the fraudulent emails you’ve received.