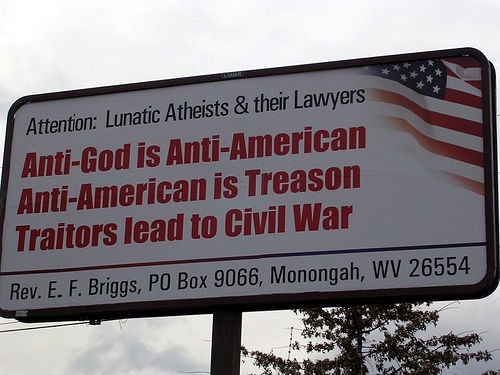
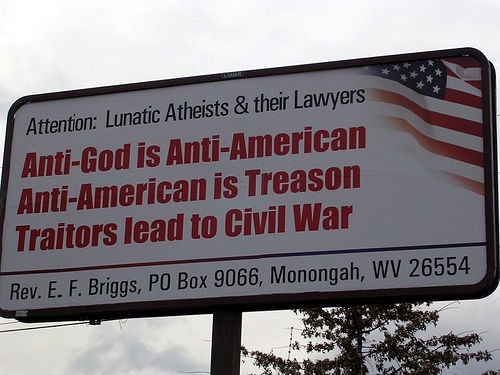
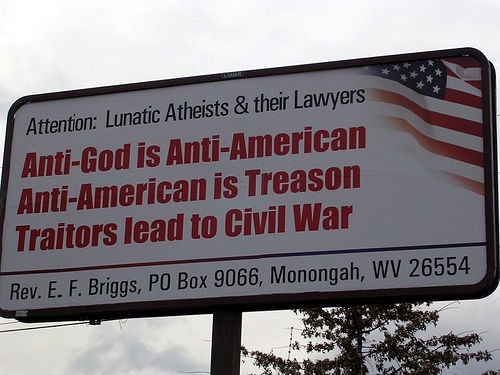
Noted without comment
132

Mac users, we had a three-month respite. The Russian Zlob gang, which last September lost its servers that were distributing the Mac DNSchanger malware when the corrupt hosting company EST Hosts went dark, are back after Macs again.
Just discovered a server being used to spread Mac malware from
*** WARNING *** WARNING *** WARNING *** This link is live as of the time of this writing. The payload, named get7003.dmg, contains a new version of the Mac DNSchanger, aka OSX.RSplug.A, OSX.RSplugin.A, or OSX/Zlob, computer malware.
The malicious server brakeplayer.net is brand new and is hosted in Latvia, on an ISP called “zlkon.lv”.
whois brakeplayer.net
Whois Server Version 2.0
Domain names in the .com and .net domains can now be registered
with many different competing registrars. Go to http://www.internic.net
for detailed information.
Domain Name: BRAKEPLAYER.NET
Registrar: REGTIME LTD.
Whois Server: whois.regtime.net
Name Server: NS1.BRAKEPLAYER.NET
Name Server: NS2.BRAKEPLAYER.NET
Status: ok
Updated Date: 26-dec-2008
Creation Date: 15-dec-2008
Expiration Date: 15-dec-2009
Name servers:
ns1.brakeplayer.net
ns2.brakeplayer.net
Registrar: Regtime Ltd.
Creation date: 2008-12-15
Expiration date: 2009-12-15
Registrant:
Nikolaj Selivestrov
Email: paul.aspen111@gmail.com
Organization: Private person
Address: ul. kosmonavtov, 132-13
City: Moskva
State: Moskovskaya
ZIP: 129301
Country: RU
Phone: +7.4957854978
I’ve also noticed an uptick in the number of hacked Web sites hosted by iPower Web lately. As I’ve talked about extensively here, here, here, and here, iPower is basically a mess. For more than a year now, hackers have been walking all over their servers, planting virus redirectors in sites that are hosted by iPower or their subsidiaries.
For a while, the number of attacks against iPower dropped to next to nothing, and I thought that they’d fixed their security problem. Now, Im not so sure–now, I think that iPower is as compromised as it always has been, but the hackers toned down the attacks when they started getting attention. Can’t prove it, but my hunch is there’s a long-standing zero-day exploit in vDeck, iPower Web’s home-grown Web control panel software.
I think we’re going to be seeing more Mac malware in the near future.